Keyloggers are commonly associated with illegal actions or purposes. What we want to say is that these are indispensable tools to talented hackers or cyber thieves. Though this attribute is a fact that cannot be denied, keylogger Mac software are also used for good intentions. For one, they are very useful in corporate set-ups where employees are monitored at all times. It is also great for home use such as in monitoring whether children using the Internet are exposed to contents not suited for their age. Whether or not this is used for protection or other (sort of) gruesome exploits, it is still good to know what keyloggers are available in the market and what they can actually do.
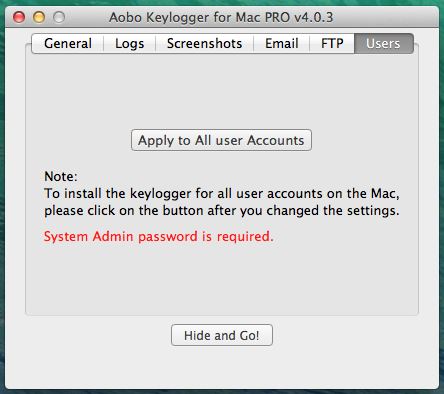
Aobo Keylogger is a small utility that can record the keystrokes captured by any Mac computer and send the logs by email or upload them to an FTP server. Moreover, Aobo Keylogger can document visited websites, chat conversations, and capture desktop screenshots. Aobo keylogger free for mac free download - Free Mac Keylogger, Perfect Keylogger Lite, Perfect Keylogger, and many more programs.
Aobo Keylogger For Mac Shortcut
10. Aobo Keylogger
Aobo does all the functions of a keylogger software. It has two types – a standard and a professional copy which essentially do the same thing. What separates the professional from the standard type is that the former can save password that are typed on a browser. It is also said that Aobo was the first to develop this kind of keylogging technique on Mac computers. It sounds very impressive and at the same time quite scary. How so? Imagine bank account passwords being given away while people doing online banking. Still, this one is worth watching.
9. AceSpy Mac
AceSpy is one decent keylogger software. It has the standard features necessary for a keylogger software and has an average user interface for easy operation. Some features of high end keylogger software are not present on this one like website blocking and keyword recognition. It also only comes in the English language.
8. BlazingTools Perfect Keylogger 2.6
Stealth mode is on and BlazingTools Perfect Keylogger is ready to hunt. This piece of software operates silently as it captures every keystroke and records virtually anything you do on your computer. This can be perfect in office setups since it can be used in monitoring employees who just keeps on skipping work and instead gets busy with personal surfing and accessing social networking sites.
7. Spector Pro
Get ready to be spied on and be placed behind bars because the sheriff is on town. Spector Pro not only has the ability to check and monitor keystrokes and instant messages, it also has the capability to block certain contacts and websites as well. What makes this software very user-friendly is that not only does it do the usual keystroke recording function, but it also automatically forwards every piece of information retained to the main operator. It can almost compare to tools being used by our friendly neighborhood law enforcement officers.
6. SniperSpy
SniperSpy makes sure that your crosshairs are pointed at the right direction for that squeky clean shot. SniperSpy is great at unraveling the truth. Spying the activities of your spouse has never been easier. Computers have been accomplices of cheating husbands and wives. SniperSpy performs the conventional keylogging method, but it also features a live feedback function. This means that anything typed or accessed in the computer being monitored is shown to the operator instantly. Another sweet feature of this software is that the operator can post an on-screen message. Gotcha!
5. BackTrack 5.1.1
BackTrack is considered as one of the most user friendly and effective keylogger software. It is also available at a decent prize. It is user friendly and the makers really gave a lot of effort in the conceptualization of this software so that it stands out from the rest. Commonly software such as this compiles the files in bulk but this one is the only one that separates the files by document and makes sure that everything is spic and span. Availing this product is a no-brainer since it costs very cheap.
4. Amac Keylogger
Amac is just the same as the other keylogger software which records and monitors everything that is accessed or opened in the computer which it is installed on. It constantly monitors every keystroke and sends it to the operator for efficient surveillance. The professional version of this can be compared with our number 10 entry, Aobo since it is said that it could also record passwords placed on various websites.
3. eBLASTER
Apprehending employees accessing forbidden websites and social networking spots is really troublesome. With eBLASTER, it is assured that nothing can get past. From files being uploaded or downloaded, to instant messages with replies, e-mail messages as well as posts from various social networking sites can be captured by this awesome software. Not even your most dramatic employee can escape the grasp of eBLASTER. This has real time notification and also the ability to block strange ID's and websites for further security and system breach issues.
2. Refog Mac
Most troubled parents are really conscious about what their kids are browsing in the Internet. Many wives and husbands also want to keep an eye on their spouse while their better halves are using the computer. For employers, it is never a waste of money just to ensure that the employees aren't just surfing the net while supposedly on the job. These are the things that Refog for Mac offers to covers. Refog is a keylogger software developed for Mac which can be used either in the house or in the office. It takes records on everything that is done to the computer without even being noticed by the user. It is password protected so that even the most techie spouse, son or employee would not be able to edit what was recorded. Anybody can use this since it has a friendly user interface that makes everything easy to operate.
1. Net Nanny for Mac
Net Nanny is mainly focused on the activities of your children while using the computer and surfing the Internet. It has a wonderful interface that parents would love to operate since nothing is complicated. Net Nanny also features live feeds and keyword blocking for a more effective parental control over your children.
All the keylogger software on this list has proven their worth in different tasks. One thing is certain—they always deliver results whether for good or ill.
Every month or so I get scam messages demanding payments in Bitcoins for the images of me they allegedly took using my webcam. They claim that they use keyloggers to control my computer.
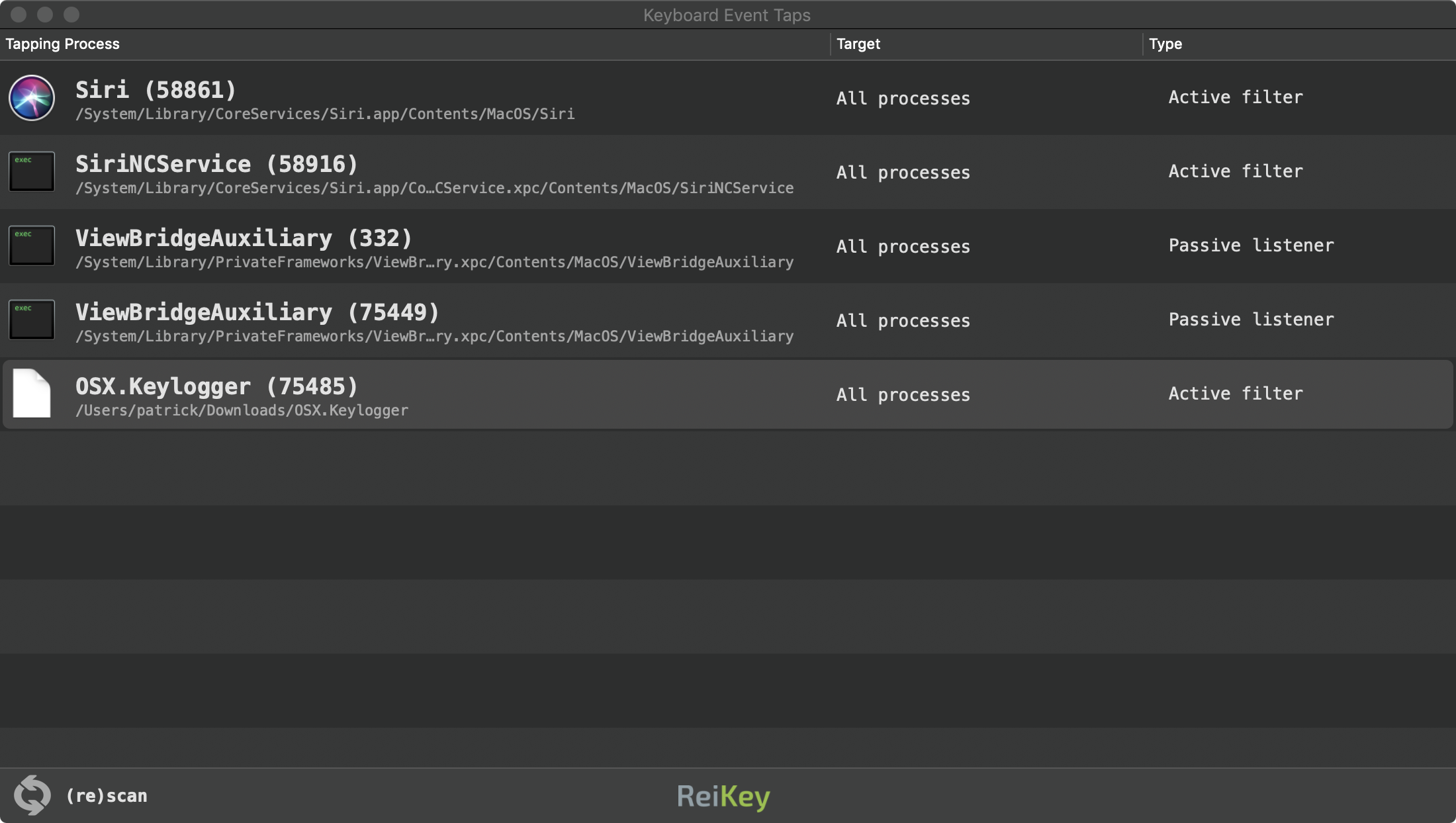
So, how to know if your Mac has a keyLogger? There are two types of keyloggers: hardware and software. Examine external USB devices connected to the Mac for hardware keyloggers. Use Activity Monitor to look for unknown processes when checking for software keylogger. Check Privacy options in System Preferences for applications with too much privileges. Install tools such as Malwarebytes and MacScan and scan computer.
How do Keyloggers Work
Keylogger or keystroke logger is a spyware application that runs invisibly for users and logs (saves on the local disk or sends to the cloud) every key that users press on the computer.
Usually, keyloggers are used by hackers to collect your credit card information you enter on various web sites. They also collect your usernames and passwords, so they can steal money from your bank accounts.

The goal of a keylogger is not to collect information for as long as possible, that's why you may never know that it was installed.
It does not suddenly slow down your computer (unless it is sending information over the internet), it does not pop up scary messages in Safari or Chrome, it does not redirect your browser to wrong web sites. It just quietly hides on your computer and gathers your data in order to use it later.
How keyloggers get installed
Typically, they get installed as part of free software you download from the Internet. The free software may contain a keylogger code inside of it so the former installs the latter on the computer.
Once installed the keyloggers starts collecting information and sends it to storage in the cloud where the hacker can access it. Keyloggers can also be installed as browser extensions.
Hardware keyloggers
There are two types of keyloggers: hardware and software. While hardware keyloggers apply mostly to desktops they are impossible to detect with the software. The hardware keylogger is usually attached to the computer and a keyboard is attached to the device.
Every time you press a key on the keyboard the device records it in its local storage and then passes the key information to the computer. If you want, you can buy a hardware keylogger on Amazon.
Software-based keystroke loggers are much more powerful because they run on the computer itself and they have access to the entire computer, not just a keyboard.
Is Keylogger Malware?
A keylogger can be either malware, like rootkit, or legitimate software installed on your computer. Commercial applications that log the keyboard input on the computer can be installed by parents who want to monitor which sites their children are visiting on the Internet. Or the company may want to track employee activities.
Believe it or not, you can easily download and install a keylogger on your own Mac. Most popular keyloggers for Mac OS are:
- Perfect Keylogger for Mac
Besides recording key presses these tools are capable of capturing screenshots, data in the clipboard, keep web browsing history.
In case of chat applications such as Skype, Viber or iMessage they can log messages from both sides: anything typed on your computer and incoming chat messages.
Some keyloggers are equipped with geolocation features. If the MacBook was stolen, they can be used to track it down because they will secretly send keystrokes and screenshots to the cloud. Keyloggers can also control your webcam and record videos or you can watch live from another computer.
You decide if it is ethical or legal to spy after children, spouse or employees. The goal of this article is to educate people about possibilities and describe ways to protect yourself from spying.
How to Install a Keylogger on Mac
To test how MacScan and Malwarebytes are capable of finding keyloggers I decided to install all four keyloggers on my Mac.
IMPORTANT: I don't endorse any keylogger here. Moreover, if you want to avoid getting malware on your Mac, do not download software from anywhere except Apple App Store. Personally, I do not trust any of the above-mentioned keyloggers, so before installing them on my MacBook I did the following:
- Took a backup of my drive
- Reset MacBook to factory settings
- Installed and tested keyloggers so I can report my findings here
- Restored everything from the backup.
There is something fundamentally sleazy about spying after other people. No wonder that installing a keylogger reminded me of installing apps with potential viruses in it.

2. Refog Mac
Most troubled parents are really conscious about what their kids are browsing in the Internet. Many wives and husbands also want to keep an eye on their spouse while their better halves are using the computer. For employers, it is never a waste of money just to ensure that the employees aren't just surfing the net while supposedly on the job. These are the things that Refog for Mac offers to covers. Refog is a keylogger software developed for Mac which can be used either in the house or in the office. It takes records on everything that is done to the computer without even being noticed by the user. It is password protected so that even the most techie spouse, son or employee would not be able to edit what was recorded. Anybody can use this since it has a friendly user interface that makes everything easy to operate.
1. Net Nanny for Mac
Net Nanny is mainly focused on the activities of your children while using the computer and surfing the Internet. It has a wonderful interface that parents would love to operate since nothing is complicated. Net Nanny also features live feeds and keyword blocking for a more effective parental control over your children.
All the keylogger software on this list has proven their worth in different tasks. One thing is certain—they always deliver results whether for good or ill.
Every month or so I get scam messages demanding payments in Bitcoins for the images of me they allegedly took using my webcam. They claim that they use keyloggers to control my computer.
So, how to know if your Mac has a keyLogger? There are two types of keyloggers: hardware and software. Examine external USB devices connected to the Mac for hardware keyloggers. Use Activity Monitor to look for unknown processes when checking for software keylogger. Check Privacy options in System Preferences for applications with too much privileges. Install tools such as Malwarebytes and MacScan and scan computer.
How do Keyloggers Work
Keylogger or keystroke logger is a spyware application that runs invisibly for users and logs (saves on the local disk or sends to the cloud) every key that users press on the computer.
Usually, keyloggers are used by hackers to collect your credit card information you enter on various web sites. They also collect your usernames and passwords, so they can steal money from your bank accounts.
The goal of a keylogger is not to collect information for as long as possible, that's why you may never know that it was installed.
It does not suddenly slow down your computer (unless it is sending information over the internet), it does not pop up scary messages in Safari or Chrome, it does not redirect your browser to wrong web sites. It just quietly hides on your computer and gathers your data in order to use it later.
How keyloggers get installed
Typically, they get installed as part of free software you download from the Internet. The free software may contain a keylogger code inside of it so the former installs the latter on the computer.
Once installed the keyloggers starts collecting information and sends it to storage in the cloud where the hacker can access it. Keyloggers can also be installed as browser extensions.
Hardware keyloggers
There are two types of keyloggers: hardware and software. While hardware keyloggers apply mostly to desktops they are impossible to detect with the software. The hardware keylogger is usually attached to the computer and a keyboard is attached to the device.
Every time you press a key on the keyboard the device records it in its local storage and then passes the key information to the computer. If you want, you can buy a hardware keylogger on Amazon.
Software-based keystroke loggers are much more powerful because they run on the computer itself and they have access to the entire computer, not just a keyboard.
Is Keylogger Malware?
A keylogger can be either malware, like rootkit, or legitimate software installed on your computer. Commercial applications that log the keyboard input on the computer can be installed by parents who want to monitor which sites their children are visiting on the Internet. Or the company may want to track employee activities.
Believe it or not, you can easily download and install a keylogger on your own Mac. Most popular keyloggers for Mac OS are:
- Perfect Keylogger for Mac
Besides recording key presses these tools are capable of capturing screenshots, data in the clipboard, keep web browsing history.
In case of chat applications such as Skype, Viber or iMessage they can log messages from both sides: anything typed on your computer and incoming chat messages.
Some keyloggers are equipped with geolocation features. If the MacBook was stolen, they can be used to track it down because they will secretly send keystrokes and screenshots to the cloud. Keyloggers can also control your webcam and record videos or you can watch live from another computer.
You decide if it is ethical or legal to spy after children, spouse or employees. The goal of this article is to educate people about possibilities and describe ways to protect yourself from spying.
How to Install a Keylogger on Mac
To test how MacScan and Malwarebytes are capable of finding keyloggers I decided to install all four keyloggers on my Mac.
IMPORTANT: I don't endorse any keylogger here. Moreover, if you want to avoid getting malware on your Mac, do not download software from anywhere except Apple App Store. Personally, I do not trust any of the above-mentioned keyloggers, so before installing them on my MacBook I did the following:
- Took a backup of my drive
- Reset MacBook to factory settings
- Installed and tested keyloggers so I can report my findings here
- Restored everything from the backup.
There is something fundamentally sleazy about spying after other people. No wonder that installing a keylogger reminded me of installing apps with potential viruses in it.
Elite Keylogger sent me to a jumpshare url, it didn't let me download from their site. The problem I had with installing Elite is that its installer did not want to close, so I had to force shutdown my Mac. Check here if you want to know more about potential issues with force shutdowns.
The Perfect Keylogger sent me two emails: one with the link from which I could download an encrypted zip file and another with the password for the zip file. Google immediately flagged both messages as dangerous spam.
Spyrix and Aobo didn't have such problems and Refog looked like a legit app with a proper installer. The interesting thing is that I was able to install all 5 of them at the same time and all four of them were recording keystrokes.
Does Malwarebytes or MacScan detect keyloggers?
Once I installed Malwarebytes it immediately recognized Elite keylogger as malware and put into quarantine. It was also able to detect Aobo and Refog. Unfortunately, it didn't find anything wrong with Perfect Keylogger and Spyrix.
MacScan was more successful: it found 4 out of 5 apps, but it still missed Perfect Keylogger.
Conclusion: If you want to install a keylogger on your Mac go with Perfect one from Blazing tools. It didn't get detected by either Malwarebytes or MacScan.
But again, do it at your own risk. If you ask my opinion, I would never install such an application on the computer where I entered my credit card information or password to my bank accounts.
On the other hand, I was disappointed with Malwarebytes and MacScan missing some apps. This experiment does not give me high confidence in malware protection tools.
So, what would I recommend you do if you believe that there is a keylogger app on your MacBook? Reset and reinstall your MacOS and immediately change all passwords for all web sites you were using.
Keylogger myths
Some people suggest a couple of workarounds that in their opinion can trick keyloggers. One of them is to use software-based keyboards. You can start such a keyboard by going to System Preferences and clicking on the 'Keyboard' icon.
In 'Input Sources' tab click on 'Show input menu in menu bar'. Once you do it you can see a keyboard icon in the top bar near the battery icon. If you click on that icon and select 'Show Keyboard Viewer' it will bring a software keyboard which you can use to type information and which supposedly will not be tracked by a keylogger.
Another workaround is to type a part of the password or the credit card number in the browser, then bring up a text editor, type a garbage text in it, switch back to the browser and type the second part of the secret password.
These workarounds possibly worked a long time ago when malware was not sophisticated, but now when they can take screenshots and have some intelligent software, I would not rely on the workarounds anymore.
How to Detect Keylogger on Mac with Activity Monitor
Some people suggest checking for malware in Activity Monitor. The typical suggestion is to bring up the Activity Monitor and find the application that looks suspicious or you do not recognize.
Theme mac for win7. This site is not directly affiliated with. DisclaimerMac OS X Theme is a product developed.
This advice may work for someone who knows all applications running on Mac, but for an average user, all applications running on Mac are unfamiliar.
I am not claiming this is impossible however. For instance, Spyrix Keylogger appear in Activity Monitor as skm, and Perfect Keylogger as DashboardClient.
What to do when getting a scam email?
Aobo Keylogger Mac Full
As said in the beginning everyone is getting emails which state that they set up malware on the certain web sites and 'your browser began working as a RDP that has a key logger which provided me access to your display as well as cam'. It continues with a threat to send embarrassing information to your friends unless 'you will make the payment via Bitcoin'.
Normally, these emails end up in a Spam folder, but if you are using an email other than Gmail chances are that they will appear in your Inbox. So, what should you do in this case? The answer is to Delete the email. This is called extortion
The hackers send such emails to millions of people with the hope that someone will be scared and will pay a ransom. They do not install keyloggers, it is cheaper to scare people by sending emails then target specific people.
How to Detect Commercial Keyloggers on Mac?
If you suspect that someone you know (your employer, spouse, parent, friend or enemy) is spying after you chances are that they installed one of the commercial keyloggers.
There is very little chance that they were able to find a malware soft built by hackers to infect your system because the malware will be sending your information to the hacker, not your personal enemy.
If you are looking to find if commercial keyloggers have been installed on your Mac, there are three ways to find: using Activity Monitor, checking default key combinations and checking the list of application with Full Disk Access.
Using Activity Monitor
Activity Monitor is still a good way to quickly find applications as long as you know their names:
- Perfect Keylogger appears as DashboardClient in the monitor
- Spyrix as skm
- Look for ‘coreservicesd' to find Aobo
- Check for ‘Elite Keylogger' when searching Elite Keylogger. However, the version I installed was free and it did not hide, so I don't know how the process name will change for someone who buys a product.
- And finally, ‘Refog' appears as ‘syslogd'
Note: there are legit services called ‘syslogd‘ and ‘coreservicesd‘, so their presence doesn't necessarily mean that you have a keylogger. To find out if the Mac was infected, scan it with the free version of Malwarebytes.
Using default key combinations
All keyloggers have secret key combinations which will bring them from the place they are hiding to the screen. After all, if you can get to the data collected by a keylogger it is pretty much useless.
Default key combinations for keyloggers are:
But, what if whoever was installing the spyware was smart enough to change the default key combination. Then you won't be able to find keyloggers by a key combination.
Aobo Keylogger For Mac Download
Check which applications have Full Disk Access
In order to do their job, most keyloggers must have full access to the disk or accessibility option.
Go to System Preferences -> Security and Privacy, click on the Privacy tab and check two sections: Accessibility and Full Disk Access.
Here how it may look like on your Mac if the app was installed:
How to Detect Malware Keystroke Loggers on Mac?
If you think that your Mac was infected by a keylogger when you've been browsing the internet or opened an email then steps above will not help because hackers do not use commercial keyloggers as malware.
You can still try to open the Activity Monitor, go over each process in it and search Google for the process name. This way, you can at least eliminate the good applications from the keyloggers (note, however, a good process can still be infected with a malware which installs a keylogger on Mac).
For instance, if you don't know what 'cloudd' process is on Mac then Google following:
cloudd mac
The first response will say something like 'This process is part of macOS and is related to iCloud'. So now you can move to the next process in the list.
Another option is to install Malwarebytes, MacScan, Intego Mac Internet Security or another antivirus and antimalware application. Some people suggested ReiKey for keystroke logger detection, but last time I checked the code was not updated for more than 8 months, which means is not being actively maintained.
And finally, the best way to get rid off a malware is remove the macOS and reinstall everything from scratch.
Other resources:
If you still feel that you are being watched then:
- buy a webcam cover: recommended webcam covers for MacBooks
- check my other article:How to Tell if Someone is Remotely Accessing Your Mac
Topics:
Image Credit: Flikr
